Introduction
This document describes how to connect a PC to a Cisco Adaptive Security Appliance (ASA) with the use of AnyConnect IPsec (IKEv2) as well as certificate and Authentication, Authorization, and Accounting (AAA) authentication.
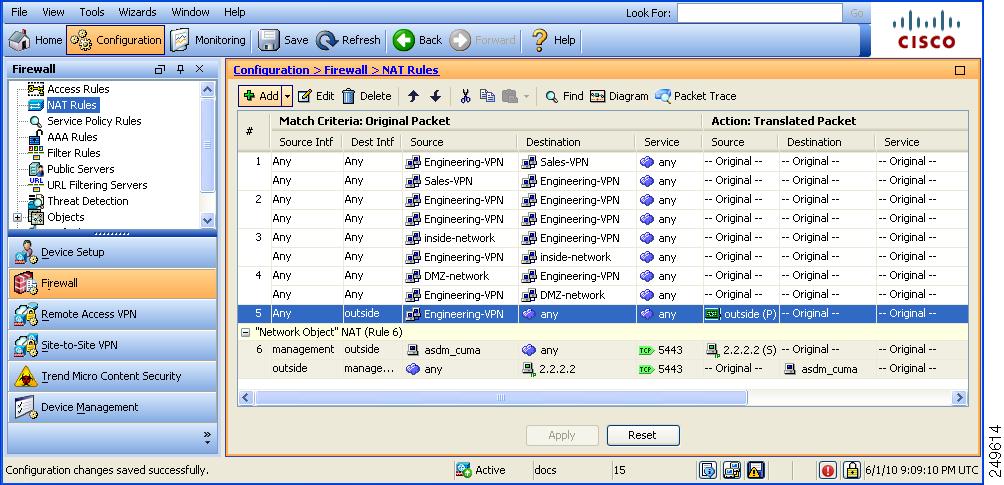
Note: The example that is provided in this document describes only the relevant parts that are used in order to obtain an IKEv2 connection between the ASA and AnyConnect. A full configuration example is not provided. Network Address Translation (NAT) or access-list configuration is not described or required in this document.
Prepare for the Connection
Anyconnect is designed to work with the ASA, and in the background, it connect automatically to the outside inteface of your firewall using HTTPS. And the firewall will be listening on that port. Remember Anyconnect will be talking to the firewall on the Outside interface, not trying to pass through the firewall.
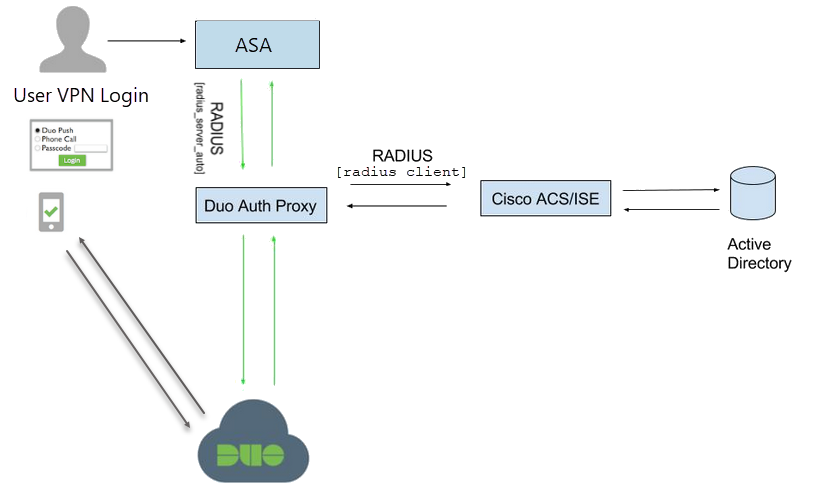
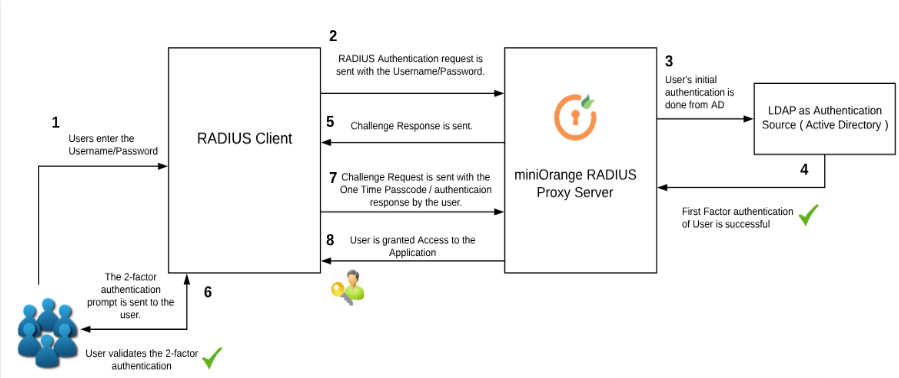
- Apr 28, 2020 As each user logs into the Cisco AnyConnect client or the Web Portal, they will enter their A ctive D irectory username and password, but then will also be required to satisfy the MFA requirement. The ASA will then assign group policies based on AD group membership, which can then be used to filter access, etc.
- “Cisco ASA Anyconnect Local CA” Means ASA act like a CA? I don’t want a group(In your example SSLUSERS) means users does not have a choice to select group from the combo box called groups. I think if I don’t need the groups I really dont’need this part ' tunnel-group MYTUNNEL webvpn-attributes '.
This section describes the perparations that are required before you can connect your PC to the ASA.
Certificates with Proper EKU
It is important to note that even though it is not required for the ASA and AnyConnect combination, RFC requires that certificates have Extended Key Usage (EKU):
- The certificate for the ASA must contain the server-auth EKU.
- The certificate for the PC must contain the client-auth EKU.
Note: An IOS router with the recent software revision can place EKUs onto certificates.
Configuration on the ASA
This section describes the ASA configurations that are required before the connection occurs.
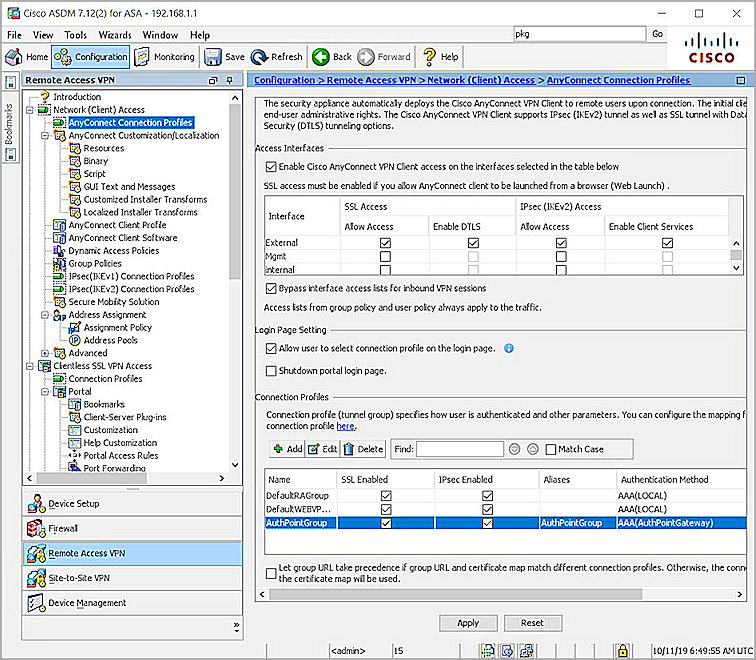
Note: The Cisco Adaptive Security Device Manager (ASDM) allows you to create the basic configuration with only a few clicks. Cisco recommends that you use it in order to avoid mistakes.
Crypto Map Configuration
Here is a crypto map example configuration:
IPsec Proposals
Here is an IPsec proposal example configuration:
IKEv2 Policies
Here is an IKEv2 policy example configuration:
Client Services and Certificate
You must enable client services and certificates on the correct interface, which is the outside interface in this case. Here is an example configuration:
Note: The same trustpoint is also assigned for Secure Sockets Layer (SSL), which is intended and required.
Enable AnyConnect Profile
You must enable the AnyConnect profile on the ASA. Here is an example configuration:
Username, Group-Policy, and Tunnel-Group
Here is an example configuration for a basic username, group-policy, and tunnel-group on the ASA:
AnyConnect Profile
Here is an example profile with the relevant parts shown in bold:
Cisco Asa Anyconnect Oid
Here are some important notes about this configuration example:
- When you create the profile, the HostAddress must match the Certificate Name (CN) on the certificate that is used for IKEv2. Enter the crypto ikev2 remote-accesstrustpoint command in order to define this.
- The UserGroup must match the name of the tunnelgroup to which the IKEv2 connection falls. If they do not match, the connection often fails and the debugs indicate a Diffie-Hellman (DH) group mismatch or a similar false negative.
Make the Connection
This section describes the PC-to-ASA connection when the profile is already present.
Note: The information that you input into the GUI in order to connect is the <HostName> value that is configured in the AnyConnect profile. In this case, bsns-asa5520-1 is entered, not the complete Fully Qualified Domain Name (FQDN).
Cisco Anyconnect Vpn Client Settings
When you first attempt to connect through AnyConnect, the gateway prompts you to select the certificate (if automatic certificate selection is disabled):
You must then enter the Username and Password:
Once the Username and Password are accepted, the connection is successful and the AnyConnect statistics can be verified:
Verification on ASA
Enter this command on the ASA in order to verify that the connection uses IKEv2 as well as AAA and certificate authentication:
Known Caveats
Cisco Asa Anyconnect Image
These are the known caveats and issues that are related to the information that is described in this document:
- The IKEv2 and SSL trustpoints must be the same.
- Cisco recommends that you use the FQDN as the CN for the ASA-side certificates. Ensure that you reference the same FQDN for the <HostAddress> in the AnyConnect profile.
- Remember to insert the <HostName> value from the AnyConnect profile when you connect.
- Even in the IKEv2 configuration, when AnyConnect connects to the ASA, it downloads profile and binary updates over SSL, but not IPsec.
- The AnyConnect connection over IKEv2 to the ASA uses EAP-AnyConnect, a proprietary mechanism that allows simpler implementation.
